13 IAM Best Practices Every SMB Should Follow
Read to learn about implementing IAM best practices to protect sensitive data, ensure compliance, and keep your organizational data safe.

How MDM Simplifies iOS Certificate Management
Are you confident in your iOS certificate management? Our guide explains automated renewals and robust protocols to secure your mobile ecosystem.

7 Ways to Streamline Your SMB’s IT Workload Management
IT workflow management is a crucial part of every SMB’s operations. Check out this guide to learn how to manage IT workflow seamlessly.
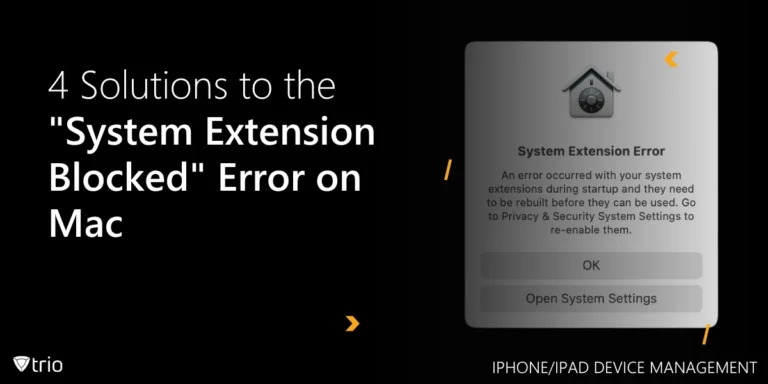
4 Solutions to the “System Extension Blocked” Error on Mac
Learn how to fix the error “System Extension Blocked” on Mac devices. This guide for IT admins includes step-by-step fixes.
Explained

13 IAM Best Practices Every SMB Should Follow
Read to learn about implementing IAM best practices to protect sensitive data, ensure compliance, and keep your organizational data safe.

How MDM Simplifies iOS Certificate Management
Are you confident in your iOS certificate management? Our guide explains automated renewals and robust protocols to secure your mobile ecosystem.

Directory Management and MDM Integration Explained
Discover expert insights on Directory Management, covering groups, active directory management, and more for IT professionals.
How-Tos

7 Ways to Streamline Your SMB’s IT Workload Management
IT workflow management is a crucial part of every SMB’s operations. Check out this guide to learn how to manage IT workflow seamlessly.
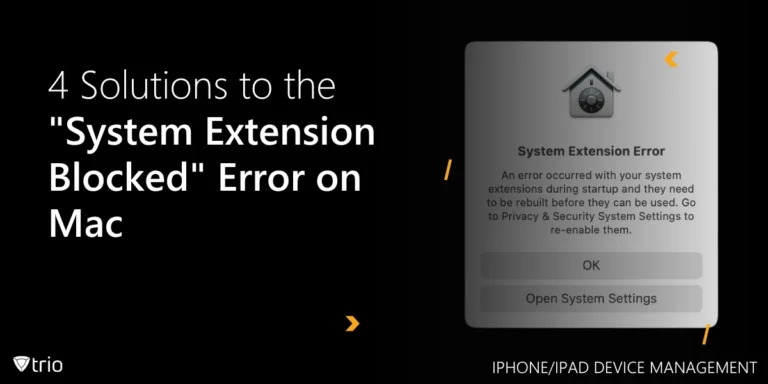
4 Solutions to the “System Extension Blocked” Error on Mac
Learn how to fix the error “System Extension Blocked” on Mac devices. This guide for IT admins includes step-by-step fixes.

Add MDM to Apple Business Manager in 5 Easy Steps
Learn how to add MDM to Apple Business Manager for faster Apple device setup, stronger security, and less IT overhead.
News

Italy Blocks DeepSeek AI Over Data Privacy Violations
Italy bans DeepSeek AI citing GDPR violations and data privacy concerns while EU nations begin investigations. Read about the regulatory implications.
FBI Removes Chinese PlugX Malware From 4,258 U.S. Computers
The FBI, with international collaboration, removed PlugX malware linked to Chinese hackers from 4,258 U.S. devices. Learn how this operation unfolded.
The Real Cost of Data Breaches for Businesses
Learn about the financial, operational, and hidden costs of data breaches in 2024. Get insights into their impacts and strategies to reduce risks effectively.
Know about news
in your inbox
Our newsletter is the perfect way to stay informed about the latest updates,
features, and news related to our mobile device management software.
Subscribe today to stay in the know and get the most out of your mobile
devices with our MDM solution app.
Product Updates
Why Trio Is the Perfect Companion for Apple Business Manager
Enhance Apple Business Manager with Trio for seamless device management, improved workflows, and top-notch security.

Streamline Notifications with Trio’s Slack Integration
Stay connected with Trio’s Slack integration—real-time alerts for security, device, and authentication updates, all in your favorite collaboration tool.

Thank You for Visiting Us at GITEX 2024!
We were excited to meet so many of you at GITEX 2024! Your enthusiasm and interest in our solutions made this an incredible experience for the entire Trio team. We […]
Templates
Ready for the TISAX Audit? Use This Checklist for Compliance
Learn about the TISAX audit process, its benefits for businesses in various industries, and a helpful checklist for achieving compliance.
Your Practical MDM Implementation Checklist for IT Admins
Make the most of your MDM solution to boost data security and operational efficiency with this easy-to-follow MDM implementation checklist.

J-SOX Compliance Requirements Checklist
Looking to meet J-SOX compliance requirements? This comprehensive checklist covers internal controls, risk assessments, and IT governance.
