One of the greatest threats to personal and corporate security is the loss or theft of mobile devices. Yet, with the remote wipe mobile device technology, you have a potent remedy to this menace.
“Remote wipe mobile device” is a security feature that allows IT administrators or device owners to issue a command that remotely deletes data from a device. It is the best solution to prevent unauthorized access to sensitive data when a device is lost or stolen. You can also employ it to remotely clear data from a device being retired or transferred to a fresh owner.
In addition to these security measures, organizations often consider MDM Migration as a strategic move to enhance their mobile device management capabilities. Migrating to a new MDM solution can streamline device management, improve security protocols, and offer advanced features to better protect mobile devices and corporate data.
The Inner Workings of Remote Wipe
The mechanics of a remote wipe are rooted in the interaction between the device and the command issued by the user or administrator. This command can be relayed via a software application or web interface, depending on the specific tool used. Upon receiving the command, the device then proceeds to erase all specified data.
The effectiveness of the remote wipe depends on the device being powered on and connected to the internet to receive the wipe command. The remote wipe may be ineffective if the device is rebooted during the process or loses connection to the internet.
The Relevance and Importance of Remote Wipe
A remote wipe protects corporate devices against physical threats to device security, such as data loss, theft, or misuse. The repercussions of not employing a remote wipe if a device is lost or stolen can be severe. If an unauthorized person gains access to the device, they can potentially extract sensitive data, leading to a data breach, financial loss, and reputational damage. Also, with the advent of remote work, corporate devices are being used outside the office premises more than ever, increasing the likelihood of these devices being lost or stolen.
The remote wipe feature comes to the rescue in such scenarios, enabling an organization to manage physical security risks effectively. By wiping lost or stolen devices, administrators can ensure their data remains secure.
Instances Where Remote Wipe Mobile Device is Essential
Remote wipe is a lifesaver in a variety of scenarios. Here are a few:
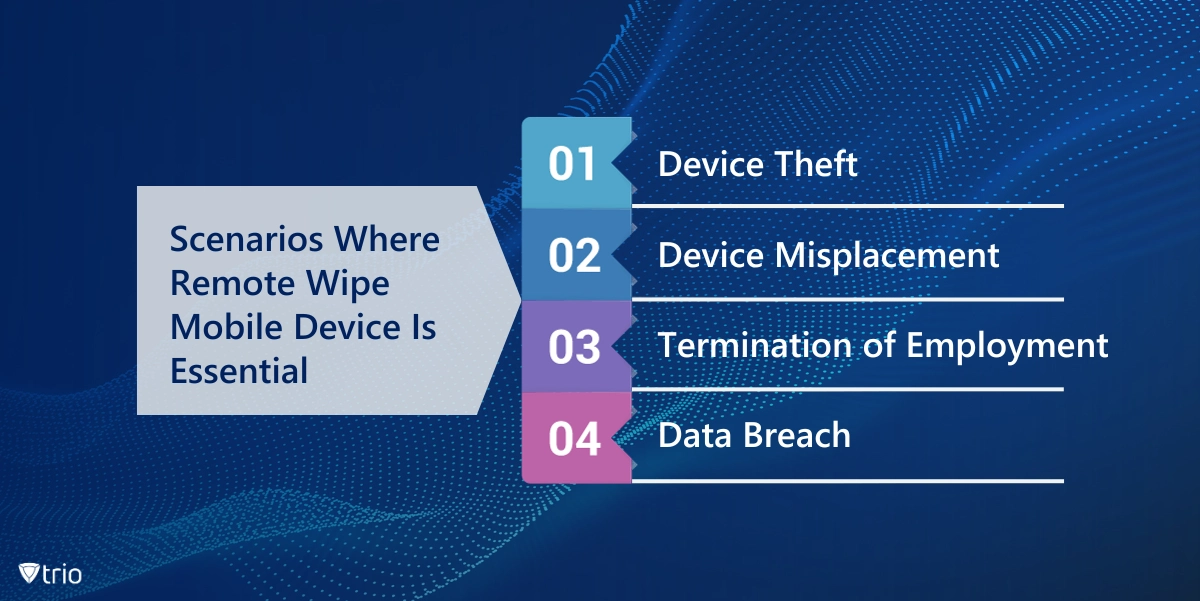
Device Theft: If an employee's device containing sensitive corporate data is stolen, you can remotely wipe it to protect the company's data.
Device Misplacement: A device that's lost can potentially land in the wrong hands, putting sensitive corporate data at risk. You can remotely wipe such devices to protect sensitive data as a precautionary measure.
Termination of Employment: When an employee leaves the company, it's essential to ensure that they no longer have access to any company-related data that might be stored on their device. A remote wipe can swiftly delete any business data from their devices. Additionally, implementing device remote locking can help prevent unauthorized access to the device, adding an extra layer of security during the transition period.
Data Breach: In the unfortunate event of a data breach, a remote wipe can be a vital damage control measure. Wiping any devices that might be compromised in the attack can minimize the damage significantly.
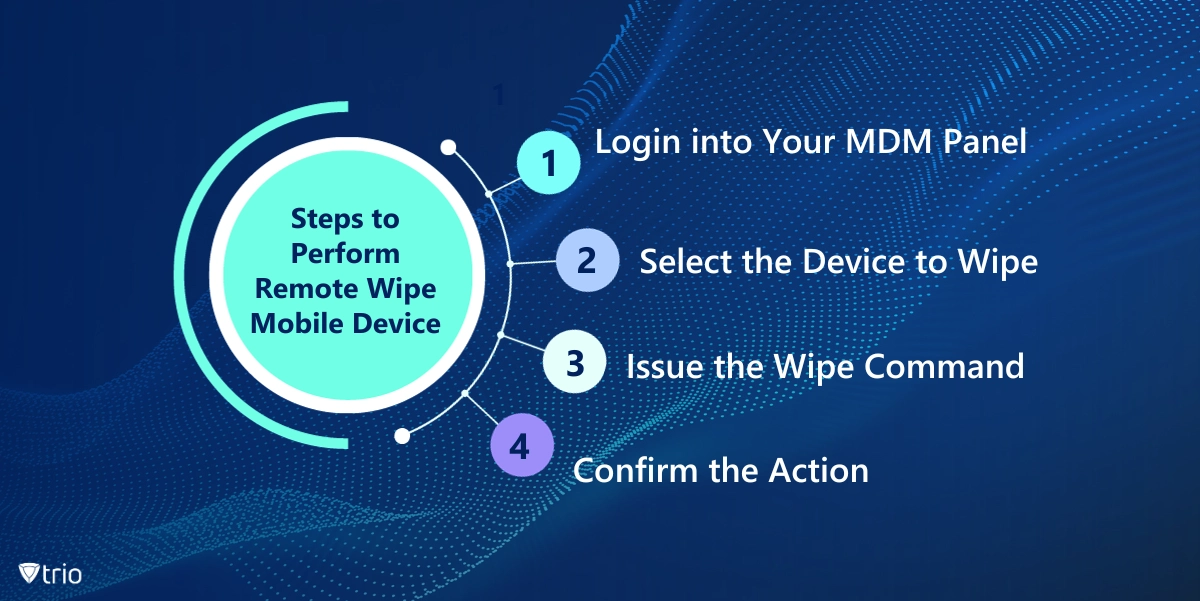
Steps to Performing Remote Wipe Mobile Device
With an MDM solution, employing a device wipe is a quick and straightforward task. It requires these simple steps:
- Login into Your MDM Panel: Log in to the admin panel of your organization's MDM software.
- Select the Device to Wipe: Navigate to view all the devices and select the one you want to wipe.
- Issue the Wipe Command: Find the option to issue a remote wipe command.
- Confirm the Action: You'll typically be asked to confirm the action since a remote wipe is irreversible. Confirm the action to initiate the remote wipe.
Best Practices for Performing Remote Wipe Mobile Device
Here are some best practices to follow when performing a remote wipe:
Ensure Devices Are Online: Remote wipes can only be performed on online devices.
Ensure Devices Are Uninterrupted: The process will fail if the devices are rebooted during the wipe. Make sure the devices remain powered on and uninterrupted during the entire process.
Have a Clear BYOD Policy: If your organization follows a Bring Your Device (BYOD) policy, ensure your remote wipe tool supports a setting that only deletes company-related data, not the employees’ data.
Educate Employees on Your Mobile Device Remote Wipe Policy: Inform employees that only company-related data will be wiped in the case of a lost device. This strategy lessens the chance that an employee won't report a lost or stolen device out of fear of losing personal data.
Use Mobile Containers: Using mobile containers to separate an employee's data from business data can make the process of wiping only work profiles and business-related data easier for IT admins.
Monitor Device Use: Keep an eye on how business services are being used on mobile devices. If a device hasn't accessed business data over a specified time, it could indicate that the device was lost or stolen. Additionally, implement access provisioning to ensure that only authorized users have access to business data and services on mobile devices, enhancing security and compliance.
The Trio MDM Solution: A Boon for IT Administrators
For IT administrators, the Trio MDM solution can be a valuable tool. It offers robust mobile device management capabilities, including the ability to perform remote wipes. This makes it easier to manage and secure devices, which is particularly useful in the context of remote work or BYOD policies.
By integrating Trio into your management strategy, you can effectively mitigate the risks associated with lost or stolen devices, thereby strengthening the organization's overall IT security posture.
- Sign up today to get a free demo.
Wrapping Up: The Benefits of Remote Wipe Mobile Device
A remote wipe mobile device is an essential tool in the IT security arsenal. It offers a potent line of defense against the loss, theft, or misuse of mobile devices, thereby protecting sensitive personal and corporate data. By understanding how it works and implementing it effectively, organizations can significantly enhance their data security and mitigate the risks associated with remote work and BYOD policies.
Get Ahead of the Curve
Every organization today needs a solution to automate time-consuming tasks and strengthen security.
Without the right tools, manual processes drain resources and leave gaps in protection. Trio MDM is designed to solve this problem, automating key tasks, boosting security, and ensuring compliance with ease.
Don't let inefficiencies hold you back. Learn how Trio MDM can revolutionize your IT operations or request a free trial today!





