According to IBM, the global average cost of a data breach in 2023 was USD 4.45 million, which is a 15% increase over the past 3 years. This is an alarming number that has caused distress among many organizations and IT professionals. Data breaches, as the name implies, occur when unauthorized individuals gain access to sensitive, confidential, or personal information. These breaches have serious consequences for businesses, including financial loss, damage to reputation, and more importantly legal implications. As a result, preventing data breaches is crucial for maintaining the security and integrity of IT infrastructure. Device management solutions are a key component of data breach prevention, as they provide organizations with the ability to secure and manage devices, enforce security policies, and protect sensitive data from unauthorized access. By implementing mobile device management (MDM) solutions, businesses can significantly reduce the risk of data breaches and ensure the safety of their digital assets. Additionally, effective IT Risk Management practices help organizations identify, assess, and mitigate potential risks to their IT systems and data, further enhancing their ability to prevent data breaches and safeguard their business operations.
Identifying Data Breaches
In order to protect organizations from the devastating effects of data breaches, businesses must prioritize the identification and analysis of potential breaches. This can be achieved through the use of data loss prevention tools and security information and event management (SIEM) systems, which can help to detect and respond to potential threats in real time. By analyzing the potential impact of data breaches on the organization, businesses can prioritize their response efforts based on the severity and potential impact of each potential threat. It’s crucial for organizations to remain vigilant in their approach to cybersecurity and data protection in order to mitigate the financial and reputational damage that can result from a data breach.
Preventing Data Breaches
There are many strategies that help organizations avoid data breaches and their horrible consequences. Some of these strategies include implementing the right security policies, especially when it comes to passwords. Organizations need to make sure they are using strong passwords, alongside activating multi-factor authentication. Data encryption also plays a vital role in protecting data both when it is being transmitted over networks as well as when it is stored on servers or other devices. It’s also important to keep all software and systems up to date with the latest security patches to prevent vulnerabilities that can be exploited by hackers. Granting access to sensitive data should be limited to employees who need it for their jobs, and access permissions should be regularly reviewed and updated. These might seem like daunting tasks, but keeping track of all of them can be a real challenge. This is exactly where device management solutions come into play and streamline the whole process.
Device management solutions play a crucial role in preventing data breaches by providing organizations with the ability to secure and manage their endpoints and applications. These solutions streamline security policies, remotely wipe data from lost or stolen devices, and monitor device usage to identify potential security risks. By implementing device management solutions, organizations can ensure that sensitive data is protected on all endpoints within their network, reducing the risk of unauthorized access and data breaches. Evaluating and selecting the best MDM solution for an organization involves a careful analysis of the organization’s needs and the features offered by different device management solutions. Businesses should consider a variety of factors including scalability, ease of use, and compatibility with existing systems to select the best solution for their specific needs. The right device management solution should offer robust security features, support for a wide range of devices, seamless integration with existing systems, and user-friendly management interfaces. Lastly, the reputation of the MDM provider and the quality of their customer support can also play a significant role in the selection process. By considering all these factors, an organization can select the MDM solution that best fits its needs and ensures the efficient and secure management of all its endpoints to target data breaches effectively.
Responding to Data Breaches
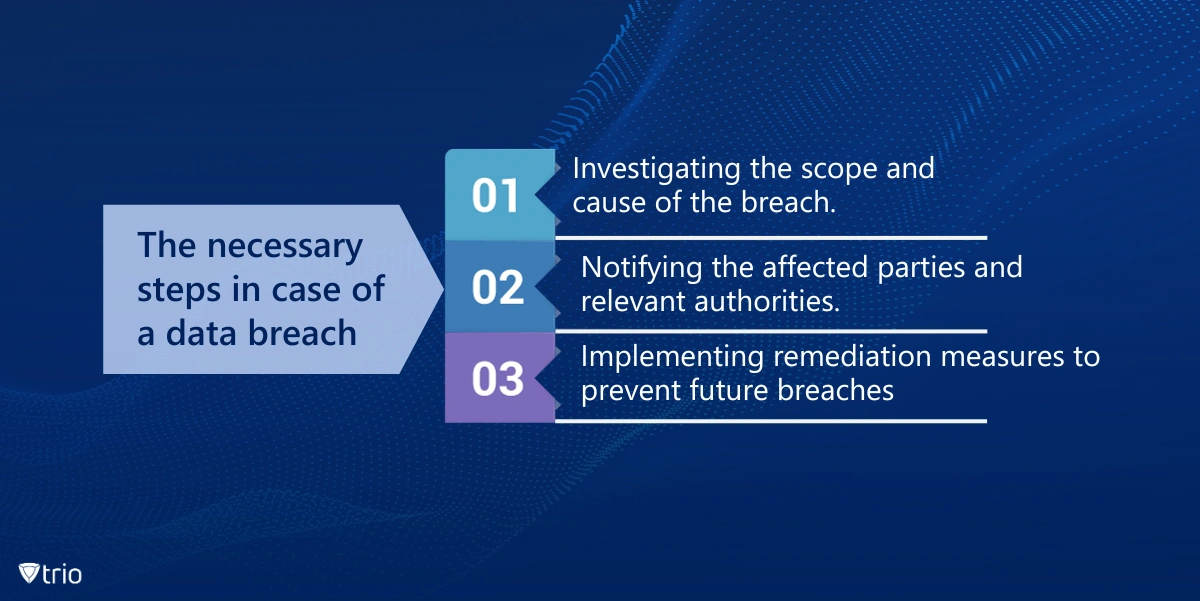
Apart from all the strategies designed to prevent data breaches, it is also important to have a data breach response plan in place. This is particularly crucial for organizations to minimize the impact of a breach and protect sensitive data. The plan should outline three important steps to take in the event of a breach: conducting an investigation to determine the scope and cause of the breach, notifying affected parties and authorities, and implementing remediation measures to prevent future breaches.
Necessary Steps to Avoid Breaches
The first step in the event of a data breach is to conduct a thorough investigation to determine the scope and cause of the breach. This involves identifying the specific systems, networks, or data that have been compromised, as well as understanding how the breach occurred and what vulnerabilities were exploited. The investigation may involve a thorough analysis of affected systems, reviewing logs and records, and even interviewing employees or third-party vendors who may have been involved. It is important to gather as much information as possible in order to understand the full extent of the breach and to later take appropriate remedial action.
Once the scope and cause of the data breach have been determined, the next step is to notify the affected parties and relevant authorities. Notification to affected parties is crucial for several reasons. First, it allows individuals to take steps to protect themselves from potential identity theft or fraud, such as monitoring their financial accounts or changing passwords. It also helps to maintain transparency and trust with customers or clients, as they have a right to know if their personal information has been put at risk. In some cases, organizations may also be required to notify regulatory bodies or government agencies, particularly if the breach involves sensitive or regulated data such as healthcare or financial information. This is often a legal requirement, and failing to do so can result in significant penalties.
The last step involves implementing remediation measures to prevent future breaches. These measures involve implementing a multi-faceted approach to fortify an organization’s cybersecurity posture. This typically includes conducting thorough security audits to identify vulnerabilities, promptly patching software and systems, and enhancing network and endpoint security. This also involves finding the right tools and device management solutions to streamline all the necessary security measures and gain invaluable insights into your IT infrastructure weaknesses. Additionally, organizations should prioritize regular employee training on cybersecurity best practices, such as recognizing phishing attempts and exercising caution when handling sensitive data.

Employee Education
Employee education plays a pivotal role in data breach prevention as employees are often the first line of defense against data breaches. Employee training and awareness programs should cover topics such as phishing scams, social engineering tactics, secure password practices, proper handling of sensitive data, and the importance of reporting any suspicious activity. These programs can be conducted through in-person training sessions, online courses, or regular reminders and updates on security best practices. Practical simulations and real-world scenarios can provide employees with hands-on experience, enabling them to develop a heightened awareness of security risks. Education on this matter should be an ongoing endeavor due to the ever-evolving nature of technology and cybersecurity threats to maintain a proactive and responsive approach against emerging risks. Additionally, organizations should also establish clear guidelines and policies for employees to follow when handling and storing personal information. This may include protocols for encrypting data, restricting access to sensitive information, and securely disposing of outdated or unnecessary records. By educating employees about the importance of data security, how to recognize potential security threats, and best practices for safeguarding sensitive information, organizations can significantly reduce the risk of human error leading to a breach.
Best Practices for Data Breach Prevention
Best practices for data breach prevention encompass several critical strategies. It’s essential to establish a comprehensive data breach prevention program, which involves creating policies, procedures, and incident response plans. Regular security assessments are vital for identifying and managing vulnerabilities
and ensuring that systems and protocols are updated effectively to address emerging threats. Implementing a device management system enhances data security by providing centralized control over all devices and ensuring compliance with security policies. Moreover, continuous improvement is paramount due to the evolving nature of cybersecurity threats. Adapting to new threats through ongoing education, implementing the latest technologies, and fostering a culture of vigilance are all integral to maintaining a strong defense against data breaches. By consistently refining preventive measures and remaining adaptable in the face of new risks, organizations can significantly strengthen their ability to mitigate potential data breaches.
Effective Targeting of Data Breaches
Trio as an MDM solution is designed to streamline all the defense strategies that are needed for a secure IT infrastructure. One of the main strategies of Trio in creating insurance against data breaches involves creating security and password policies to ensure all devices are secure at all times. Through Trio’s password policies, users can bolster their passwords with varying levels of complexity, enhancing the overall strength of their access credentials. Furthermore, the capability to activate multi-factor authentication provides an added layer of protection against unauthorized access. Trio facilitates ongoing device auditing, ensuring consistent oversight of all connected endpoints. This, in combination with seamless patch updating, serves to proactively address any potential vulnerabilities, minimizing the risk of exploitation and fortifying the network against potential data breaches.
It's evident that organizations must be prepared to respond effectively to data breaches, in addition to implementing preventative measures. This involves having a robust data breach response plan that outlines investigative steps, notifications, and remediation measures. An efficient investigation allows for a thorough understanding of the breach, shaping subsequent actions regarding affected parties and regulatory bodies. Beyond this, implementing remediation measures, including comprehensive security audits, software patching, and employee education, is integral to further bulletproofing an organization's cybersecurity posture. Additionally, having cybersecurity insurance in place can provide financial protection and support in the event of a data breach or cyber incident. This multifaceted approach, integrated with suitable tools and device management solutions, ensures a more resilient security infrastructure.
Get Ahead of the Curve
Every organization today needs a solution to automate time-consuming tasks and strengthen security.
Without the right tools, manual processes drain resources and leave gaps in protection. Trio MDM is designed to solve this problem, automating key tasks, boosting security, and ensuring compliance with ease.
Don't let inefficiencies hold you back. Learn how Trio MDM can revolutionize your IT operations or request a free trial today!