Remote server management services are an essential component of modern IT infrastructure, offering a plethora of benefits in managing an organization's servers remotely. They encompass a wide range of tasks, from system installation and configuration to security management and performance optimization. This article provides an in-depth exploration of remote server management services, highlighting the benefits, examples of remote servers, best practices for server access, and the role of remote server monitoring software in ensuring seamless server operations.
Understanding Remote Server Management Services
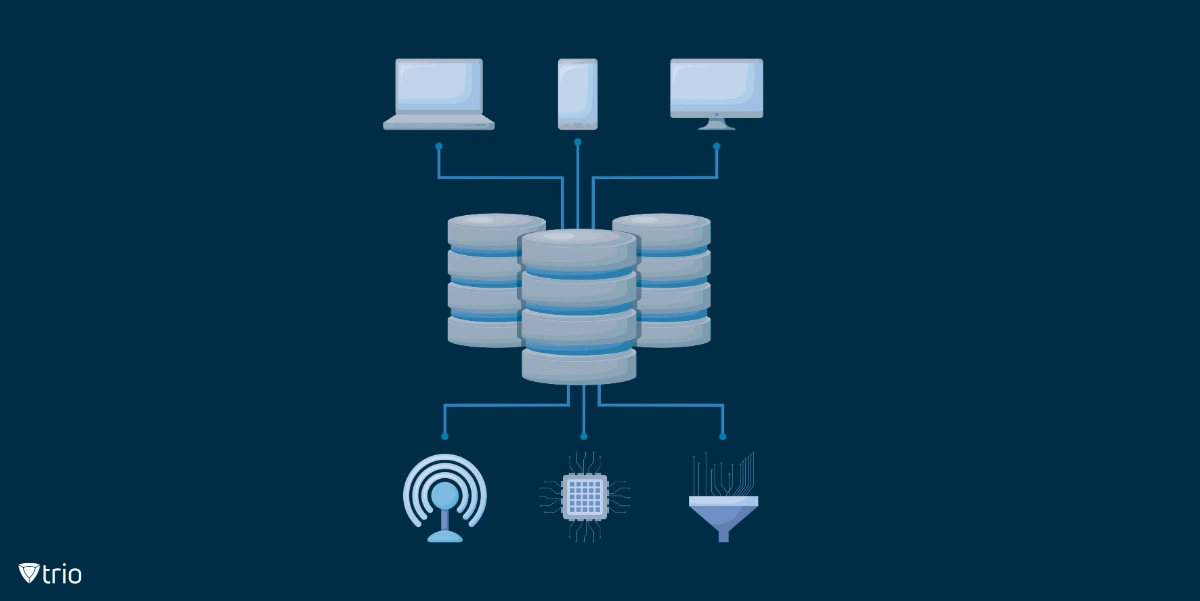
Remote server management services refer to the suite of tasks and operations aimed at overseeing the functionality, maintenance, and optimization of server systems within an organization's IT infrastructure. By leveraging these services, organizations can ensure high availability, enhanced performance, and robust security of their servers, irrespective of their physical location.
The Scope of Remote Server Management Services
Remote server management services cover a broad spectrum of tasks, including:
Installation and Configuration: This involves setting up new servers with the appropriate operating systems, software, and configurations based on the organization's requirements.
Security Management: Implementing robust security measures such as firewalls, encryption, and access controls is crucial in protecting servers against unauthorized access, data breaches, and other cyber threats.
Performance Monitoring and Optimization: Monitoring server performance metrics like CPU usage, memory utilization, and disk I/O helps identify potential bottlenecks and performance issues, enabling prompt optimization of server resources.
Backup and Disaster Recovery: Implementing effective backup solutions and crafting disaster recovery plans ensure business continuity in the event of server failures or data loss.
Patch Management: Regular application of software patches, updates, and security fixes is vital to address vulnerabilities, bugs, and other issues, ensuring servers run the latest and most secure software versions.
User Management: This includes managing user accounts, permissions, and access rights to ensure only authorized users have access to server resources and data.
Capacity Planning: Forecasting future resource requirements based on current usage trends and expected growth is crucial for planning server upgrades or expansions, ensuring scalability.
Troubleshooting and Problem Resolution: Diagnosing and resolving server-related issues like hardware failures, software errors, and network connectivity problems helps minimize downtime and maintain service availability.
Remote Servers Examples
Remote servers range from web servers and database servers to file servers and virtual servers. Each type of server is designed to fulfill specific functions within an organization's IT infrastructure.
Web Servers
Web servers host websites and web applications, responding to client requests for web pages and delivering content over the internet using HTTP and HTTPS protocols.
Database Servers
Database servers store, manage, and provide access to databases, enabling users and applications to store, retrieve, and manipulate data.
File Servers
File servers store and manage files and directories, providing centralized storage and access control within an organization's network. They enable users to share files, collaborate on documents, and access shared resources.
Application Servers
Application servers host and execute applications, providing runtime environments and services for running application code.
Virtual Servers
Virtual servers host virtual machines (VMs) or containers, allowing multiple virtualized operating systems and applications to run on a single physical server hardware.
Best Practices for Remote Server Access on Windows and Linux
To maintain secure and efficient remote server access on Windows and Linux, organizations should follow several best practices:
Secure Connections: Always use secure connections like SSH (Secure Shell) for Linux and RDP (Remote Desktop Protocol) for Windows to access your servers remotely. These protocols encrypt data in transit, ensuring secure communication.
Multi-Factor Authentication: Implementing multi-factor authentication adds an extra layer of security, making it harder for unauthorized users to gain access to your servers.
Regular Patching and Updating: Regularly update and patch your servers to protect them from potential security vulnerabilities. This includes updating the operating system, installed software, and security configurations.
Monitoring and Logging: Implement monitoring and logging to track server performance and user activities. This can help you identify potential issues early and provide valuable insights for troubleshooting.
User and Access Management: Manage user accounts and access permissions carefully to ensure that only authorized individuals have access to your servers.

The Criticality of Remote Server Monitoring Software
Remote server monitoring software plays a pivotal role in managing the health and performance of servers. It offers real-time monitoring capabilities, allowing IT administrators to track critical server metrics such as CPU usage, memory utilization, disk space, network traffic, and more. By promptly identifying potential issues, remote server monitoring software helps reduce downtime, optimize server performance, and enhance overall system reliability.
The Role of Mobile Device Management in Remote Server Management
In the era of mobile computing, mobile device management (MDM) has emerged as a crucial element in remote server management. MDM solutions, such as Trio's MDM solution, provide IT administrators with the tools to manage and secure mobile devices accessing the server remotely. Trio offers a range of features, including device tracking, app management, remote lock and wipe, and much more. By integrating the Trio MDM solution into their remote server management strategy, your organization can ensure secure and efficient server access from mobile devices, thereby enhancing IT security and productivity.
To witness firsthand the positive impact such a system can have on your operation, we invite you to try out Trio’s free demo and see how you can make a difference in IT automation at your organization.
Conclusion: The Importance of Remote Server Management Services
Remote server management services are an indispensable tool for modern IT infrastructure management. They enable organizations to maintain high availability, enhanced performance, and robust security of their servers. With the advent of mobile device management solutions like Trio's MDM solution, organizations can further augment their server management strategies, ensuring secure and efficient server access from mobile devices. As technology continues to evolve, staying abreast of the latest trends and best practices in server management is crucial for organizations aiming to maintain a robust and resilient IT infrastructure.
Get Ahead of the Curve
Every organization today needs a solution to automate time-consuming tasks and strengthen security.
Without the right tools, manual processes drain resources and leave gaps in protection. Trio MDM is designed to solve this problem, automating key tasks, boosting security, and ensuring compliance with ease.
Don't let inefficiencies hold you back. Learn how Trio MDM can revolutionize your IT operations or request a free trial today!





